📃Title: Game of Emperor: Unveiling Long Term Earth Estries Cyber Intrusions
📅Date: 2024-11-25
🔗References:
- https://www.trendmicro.com/en_us/research/24/k/earth-estries.html
- https://www.trendmicro.com/content/dam/trendmicro/global/en/research/24/k/earth-estries/IOC_list-EarthEstries.txt
- https://x.com/_rectifyq/status/1861077973727895669
Description
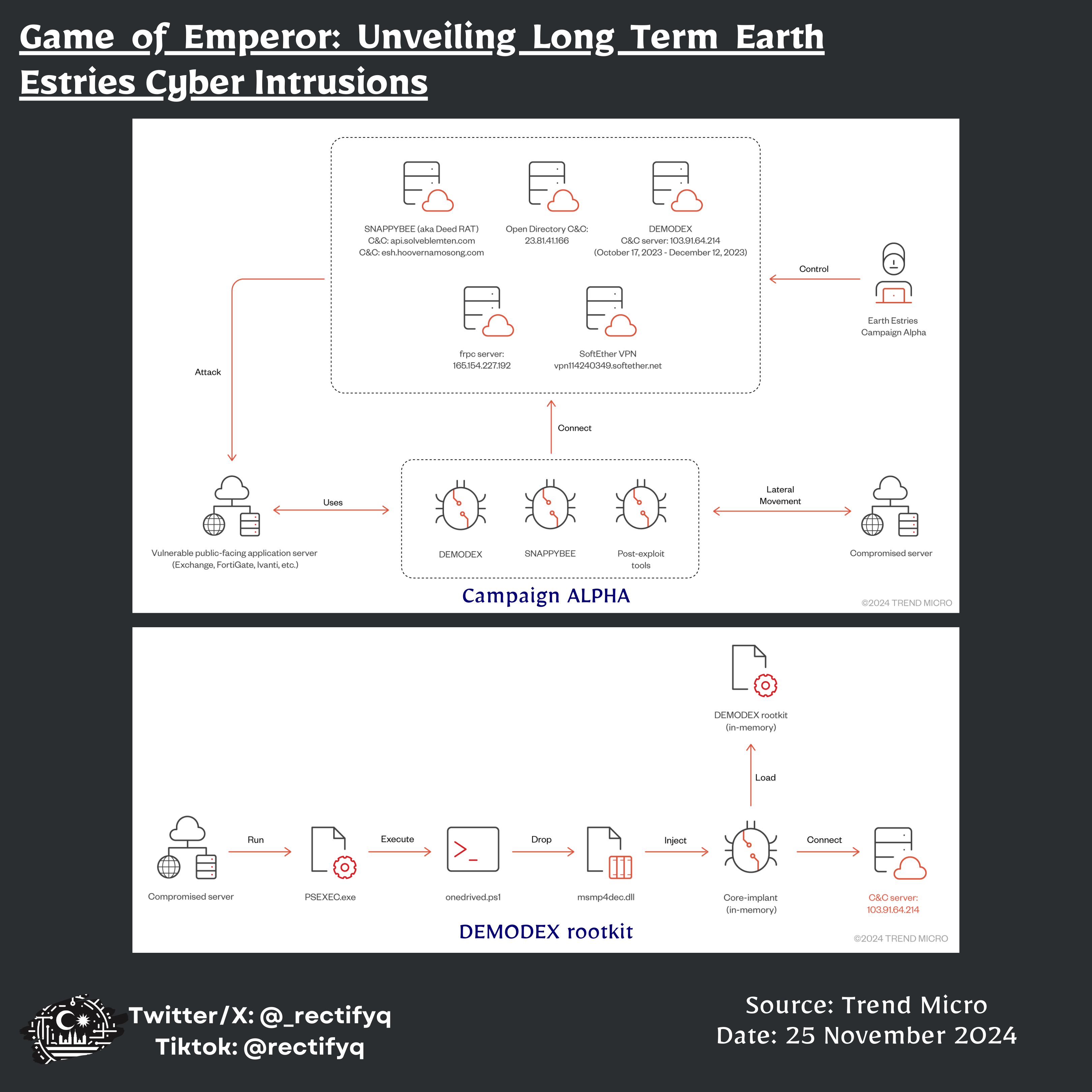
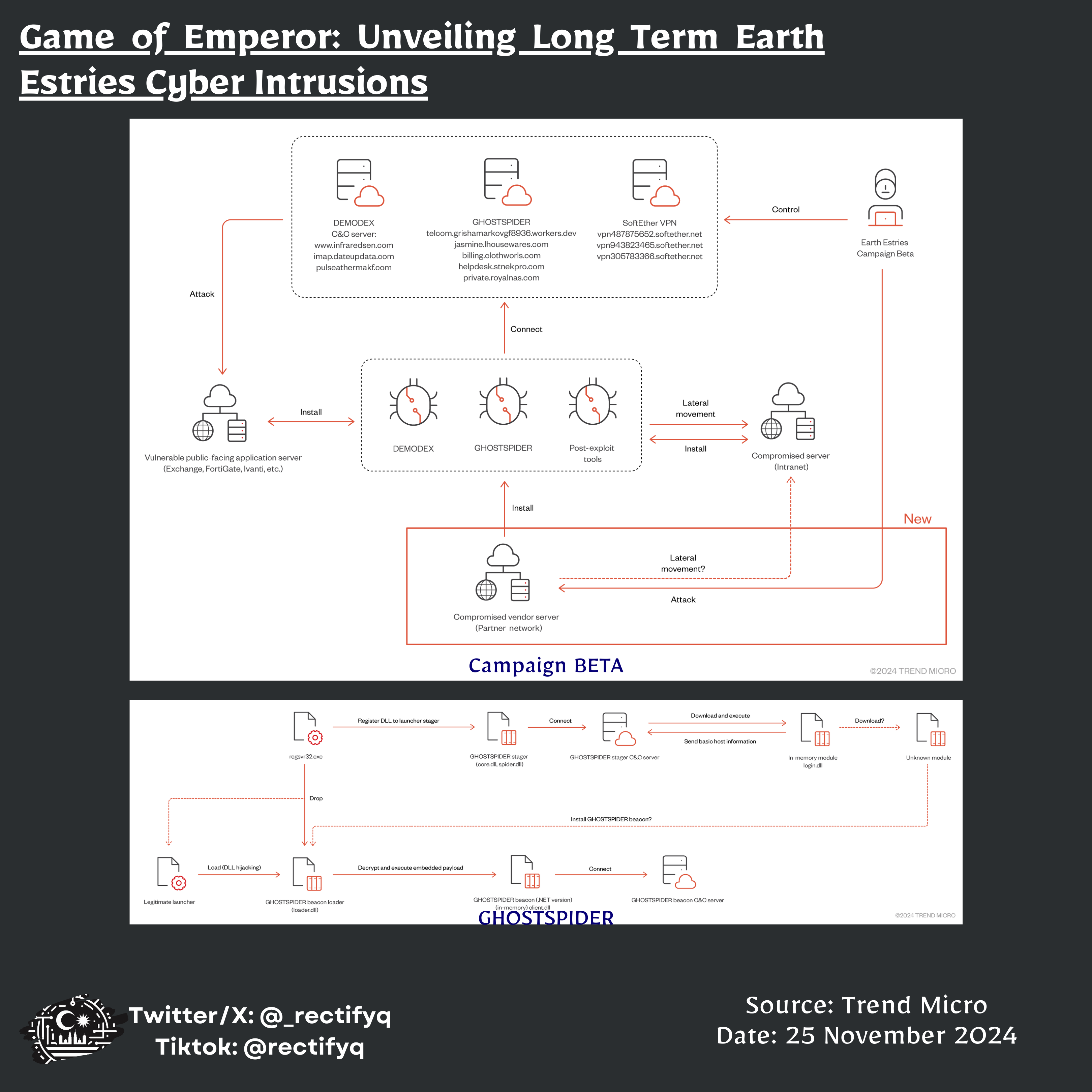
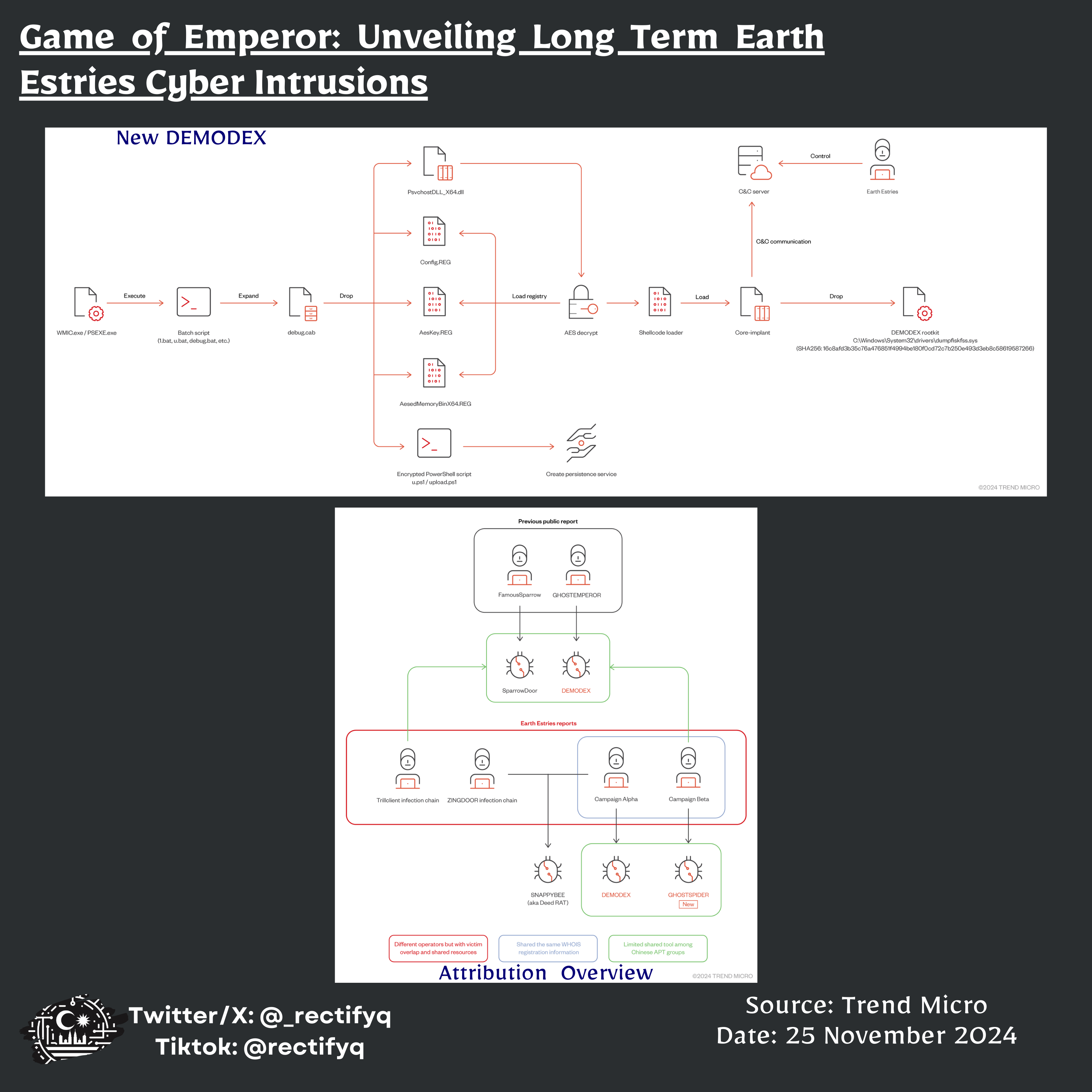
Earth Estries, a Chinese APT group, has been aggressively targeting critical sectors globally since 2023. The group employs advanced techniques and multiple backdoors, including GHOSTSPIDER, SNAPPYBEE, and MASOL RAT, to compromise organizations in telecommunications, government, and other industries across various countries. Their sophisticated attacks exploit server vulnerabilities for initial access and use living-off-the-land binaries for lateral movement. Earth Estries has successfully infiltrated over 20 organizations, demonstrating a complex C&C infrastructure and possible shared tools with other Chinese APT groups. The group’s operations involve long-term espionage activities, targeting not only critical services but also vendor networks to facilitate broader access.
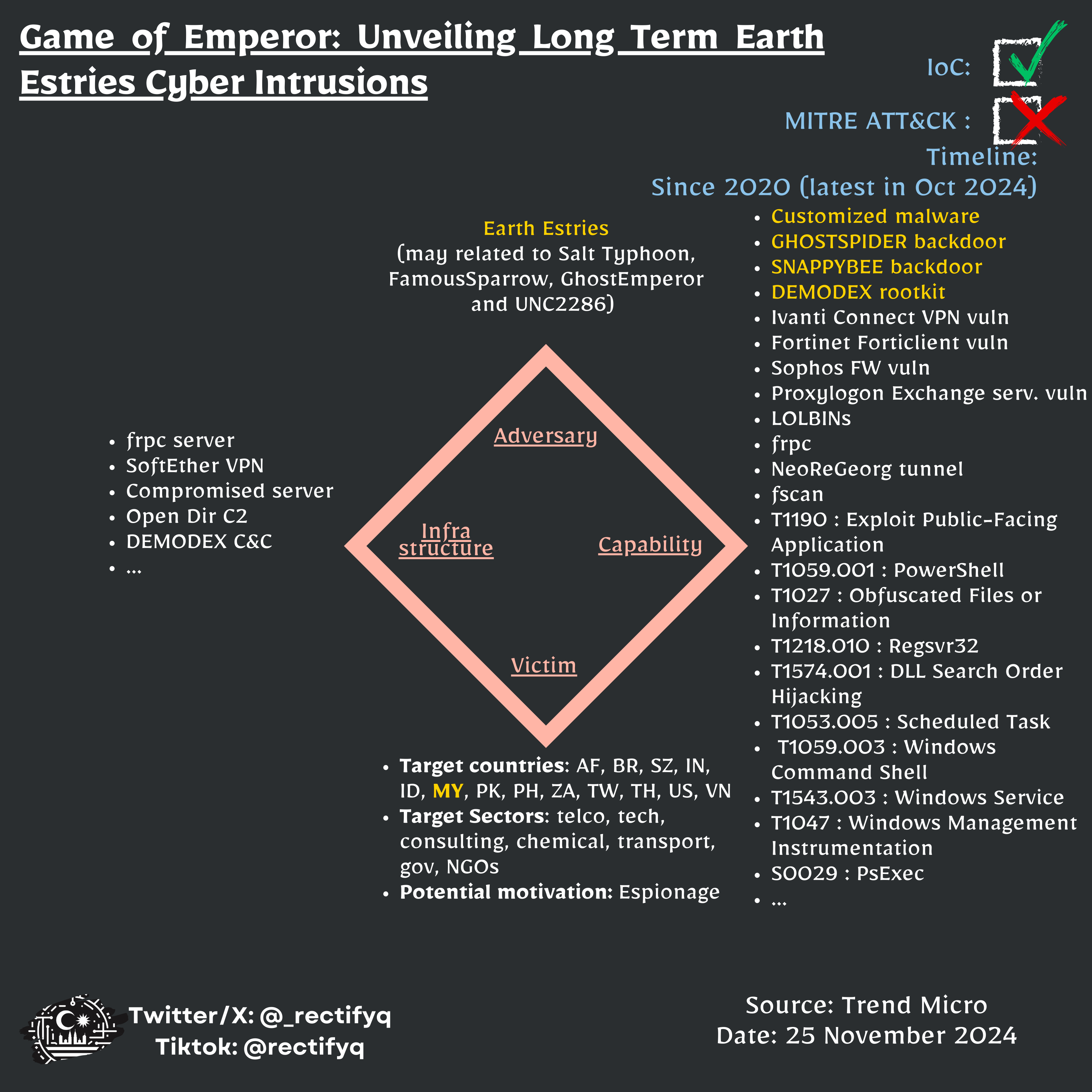
🔖Rectifyq Taxonomies:
- relevancy: 🔴 Highly Relevant
- category: ⚔Threat
- sub-category: TA-profile
- target: targeted
- MY-relevancy: relevant
- action-taken: diamond-model
🔖MISP Galaxies:
- producer= Trend-Micro
- target-information=“Afghanistan”
- target-information=“Brazil”
- target-information=“British Indian Ocean Territory”
- target-information=“India”
- target-information=“Indonesia”
- target-information=“Malaysia”
- target-information=“Pakistan”
- target-information=“Philippines”
- target-information=“South Africa”
- target-information=“Taiwan”
- target-information=“Thailand”
- threat-actor= Earth-Estries
- sector=“Chemical”
- sector=“Consulting”
- sector=“Government, Administration”
- sector=“NGO”
- sector=“Technology”
- sector=“Telecoms”
- sector=“Transport”
- mitre-tool=“PsExec - S0029”
- target-information=“Swaziland”
- country=“china”
- mitre-attack-pattern=[‘T1132.001’, ‘T1003’, ‘T1133’, ‘T1082’, ‘T1053’, ‘T1140’, ‘T1190’, ‘T1055’, ‘T1021.002’, ‘T1112’, ‘T1505.003’, ‘T1016’, ‘T1083’, ‘T1059.001’, ‘T1078’, ‘T1068’, ‘T1027’, ‘T1102.002’, ‘T1573.002’, ‘T1071.001’]
MISP event uuid: 05866c45-7c9e-4481-ae50-60471a9c91ed
Indicator of Compromise (IoCs)
type,value,comment
md5, 8bd8506f6b1a80eea68e877fa81e267c, 'SNAPPYBEE loader'
md5, 334c9477f71802c57349a997b8bf6d61, 'SNAPPYBEE payload'
md5, 3f98cc479ee574320dc5dabb67c56c94, 'DEMODEX PowerShell dropper'
md5, 505b55c2b68e32acb5ad13588e1491a5, 'SNAPPYBEE loader'
md5, 43f3f328248da7bda95407968604ff0b, 'SNAPPYBEE loader'
md5, 45d7997340065904ae092ac427c54f41, 'SNAPPYBEE loader'
md5, b706f4806dc88611873cadeb3ad1ff97, 'SNAPPYBEE payload'
ip-dst, 103.91.64.214, 'Campaign Alpha (DEMODEX)'
ip-dst, 165.154.227.192, 'Campaign Alpha (frpc)'
ip-dst, 23.81.41.166, 'Campaign Alpha (Open directory C&C)'
ip-dst, 158.247.222.165, 'Campaign Alpha (SNAPPYBEE)'
ip-dst, 172.93.165.14, 'Campaign Alpha (related C&C)'
ip-dst, 91.245.253.27, 'Campaign Alpha (SNAPPYBEE)'
ip-dst, 103.75.190.73, 'Campaign Alpha (related C&C)'
ip-dst, 45.125.67.144, 'Campaign Beta (DEMODEX)'
ip-dst, 43.226.126.164, 'Campaign Beta (DEMODEX)'
ip-dst, 172.93.165.10, 'Campaign Beta (DEMODEX)'
ip-dst, 193.239.86.168, 'Campaign Beta (DEMODEX)'
ip-dst, 146.70.79.18, 'Campaign Beta (DEMODEX)'
ip-dst, 146.70.79.105, 'Campaign Beta (DEMODEX)'
ip-dst, 205.189.160.3, 'Campaign Beta (DEMODEX)'
ip-dst, 96.9.211.27, 'Campaign Beta (DEMODEX)'
ip-dst, 43.226.126.165, 'Campaign Beta (DEMODEX)'
ip-dst, 139.59.108.43, 'Campaign Beta (GHOSTSPIDER)'
ip-dst, 185.105.1.243, 'Campaign Beta (GHOSTSPIDER)'
ip-dst, 143.198.92.175, 'Campaign Beta (GHOSTSPIDER)'
ip-dst, 139.99.114.108, 'Campaign Beta (GHOSTSPIDER)'
ip-dst, 139.59.236.31, 'Campaign Beta (GHOSTSPIDER)'
ip-dst, 104.194.153.65, 'Campaign Beta (GHOSTSPIDER)'
domain, materialplies.com, 'Campaign Alpha (related C&C)'
hostname, news.colourtinctem.com, 'Campaign Alpha (related C&C)'
hostname, api.solveblemten.com, 'Campaign Alpha (SNAPPYBEE)'
hostname, esh.hoovernamosong.com, 'Campaign Alpha (SNAPPYBEE)'
hostname, vpn114240349.softether.net, 'Campaign Alpha (SoftEther VPN)'
hostname, imap.dateupdata.com, 'Campaign Beta (DEMODEX)'
domain, pulseathermakf.com, 'Campaign Beta (DEMODEX)'
hostname, www.infraredsen.com, 'Campaign Beta (DEMODEX)'
hostname, billing.clothworls.com, 'Campaign Beta (GHOSTSPIDER)'
hostname, helpdesk.stnekpro.com, 'Campaign Beta (GHOSTSPIDER)'
hostname, jasmine.lhousewares.com, 'Campaign Beta (GHOSTSPIDER)'
hostname, private.royalnas.com, 'Campaign Beta (GHOSTSPIDER)'
hostname, telcom.grishamarkovgf8936.workers.dev, 'Campaign Beta (GHOSTSPIDER)'
hostname, vpn305783366.softether.net, 'Campaign Beta (SoftEther VPN)'
hostname, vpn487875652.softether.net, 'Campaign Beta (SoftEther VPN)'
hostname, vpn943823465.softether.net, 'Campaign Beta (SoftEther VPN)'
sha256, 16c8afd3b35c76a476851f4994be180f0cd72c7b250e493d3eb8c58619587266, 'DEMODEX driver No sample in VT\r\nLast check:01/05/2025'
sha256, 9ba31dc1e701ce8039a9a272ef3d55aa6df66984a322e0d309614a5655e7a85c, 'DEMODEX loader No sample in VT\r\nLast check:01/05/2025'
sha256, 6d64643c044fe534dbb2c1158409138fcded757e550c6f79eada15e69a7865bc, 'SNAPPYBEE loader No sample in VT\r\nLast check:01/05/2025'
Full IOCs available in Rectifyq’s MISP