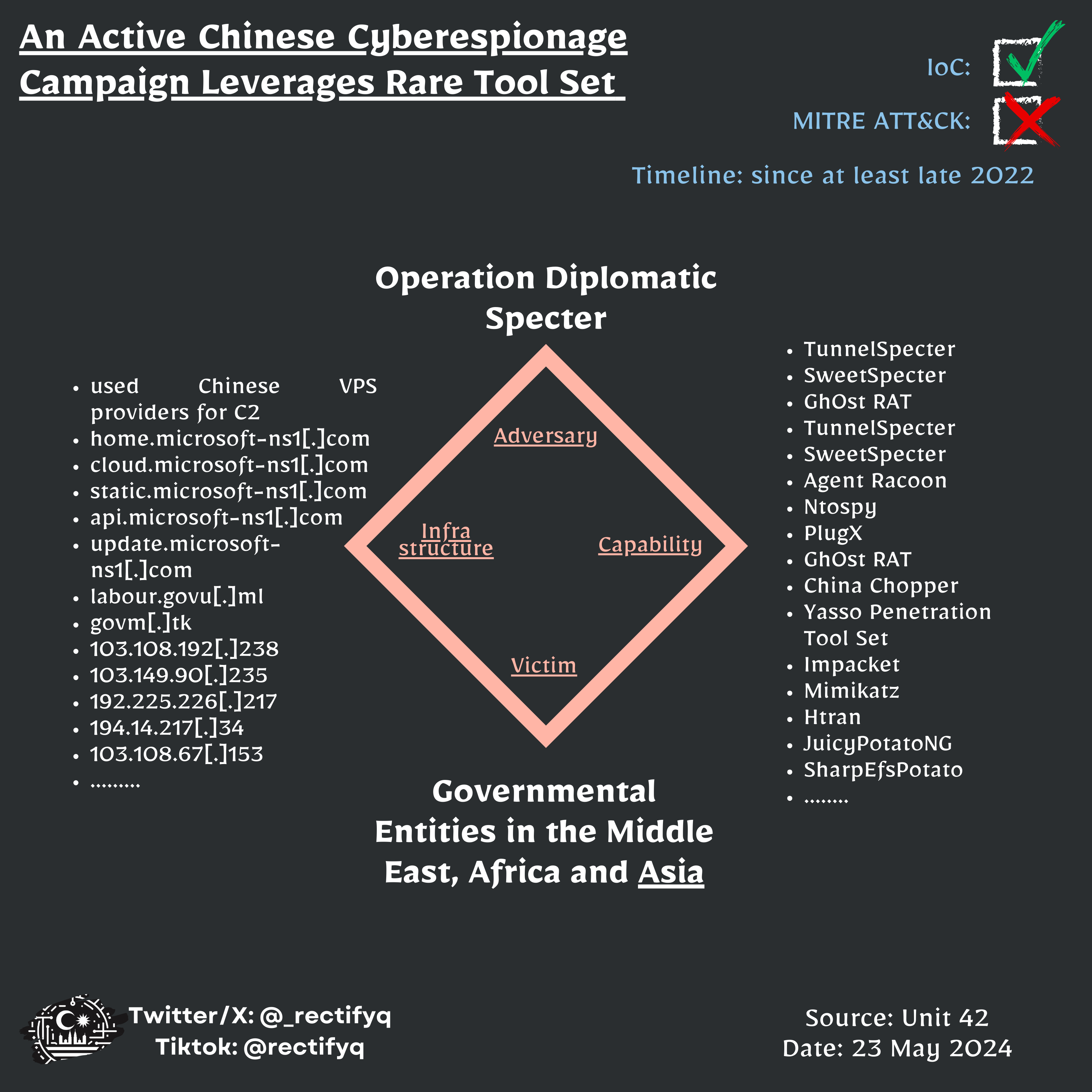
📃Title: Operation Diplomatic Specter: An Active Chinese Cyberespionage Campaign Leverages Rare Tool Set to Target Governmental Entities in the Middle East, Africa and Asia
📅Date: 2024-05-23
🔗References:
🔖Rectifyq Taxonomies:
- relevancy: 🟡 Somewhat Relevant
- category: ⚔Threat
- sub-category: campaign-analysis
- topic: geopolitical
- target: broad-based
- MY-relevancy: somewhat-relevant
- action-taken: diamond-model
🔖MISP Galaxies:
- producer= Palo-Alto
- region=“002 - Africa”
- region=“142 - Asia”
- sector=“Diplomacy”
- sector=“Military”
- sector=“Political party”
- threat-actor= APT27
- threat-actor= APT41
- threat-actor= MUSTANG-PANDA
- malpedia=“CHINACHOPPER”
- malpedia=“Ghost RAT”
- malpedia=“HTran”
- malpedia=“PlugX”
- mitre-attack-pattern=[]
MISP event uuid: 2e091577-f7df-47ed-a59f-07e5eb07b7a7
Indicator of Compromise (IoCs)
type,value,comment
sha256, 0e0b5c5c5d569e2ac8b70ace920c9f483f8d25aae7769583a721b202bcc0778f, 'TunnelSpecter - Loader'
sha256, 62dec3fd2cdbc1374ec102d027f09423aa2affe1fb40ca05bf742f249ad7eb51, 'TunnelSpecter - Encrypted payload'
sha256, 22d556db39bde212e6dbaa154e9bcf57527e7f51fa2f8f7a60f6d7109b94048e, 'TunnelSpecter - Decrypted payload'
sha256, 0b980e7a5dd5df0d6f07aabd6e7e9fc2e3c9e156ef8c0a62a0e20cd23c333373, 'SweetSpecter - Loader'
sha256, 8198c8b5eaf43b726594df62127bcb1a4e0e46cf5cb9fa170b8d4ac2a4dad179, 'SweetSpecter - Encrypted payload'
sha256, 0f72e9eb5201b984d8926887694111ed09f28c87261df7aab663f5dc493e215f, 'SweetSpecter - Decrypted payload'
sha256, d5a44380e4f7c1096b1dddb6366713aa8ecb76ef36f19079087fc76567588977, 'Gh0st RAT'
hostname, home.microsoft-ns1.com, ''
hostname, cloud.microsoft-ns1.com, ''
hostname, static.microsoft-ns1.com, ''
hostname, api.microsoft-ns1.com, ''
hostname, update.microsoft-ns1.com, ''
hostname, labour.govu.ml, ''
domain, govm.tk, ''
ip-dst, 103.108.192.238, ''
ip-dst, 103.149.90.235, ''
ip-dst, 192.225.226.217, ''
ip-dst, 194.14.217.34, ''
ip-dst, 103.108.67.153, ''
Full IOCs available in Rectifyq’s MISP