📃Title: Tria stealer targets Android users for SMS exfiltration and financial gain
📅Date: 2025-01-30
🔗References:
Description
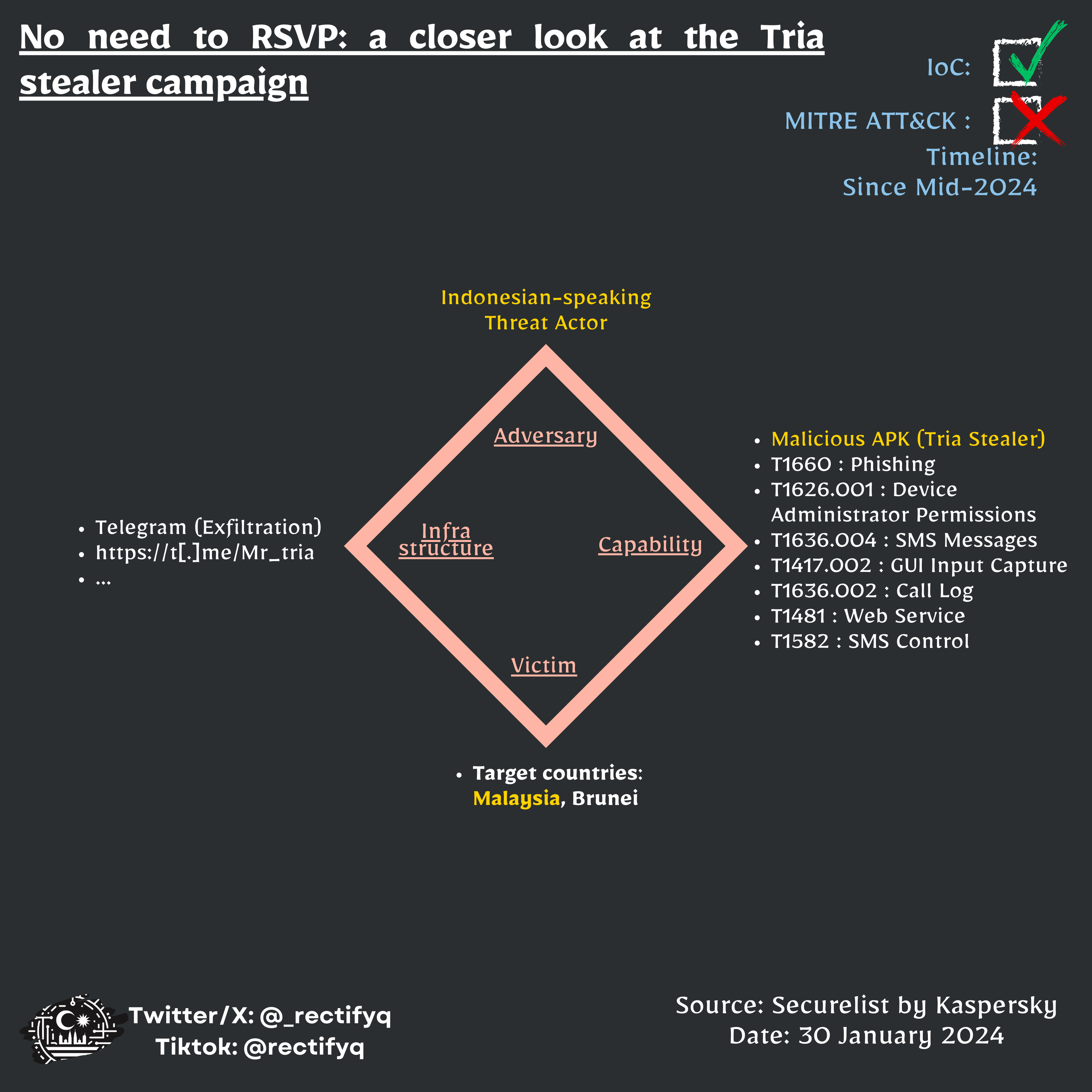
Since mid-2024, a malicious Android campaign dubbed ‘Tria Stealer’ has been targeting users in Malaysia and Brunei using wedding invitation lures. The malware collects SMS data, call logs, messages from apps like WhatsApp, and email data from Gmail and Outlook. It exfiltrates this information to Telegram bots used as C2 servers. The threat actor exploits the stolen data to hijack personal messaging accounts, impersonate victims to request money transfers, and compromise other accounts. The campaign is likely operated by an Indonesian-speaking threat actor based on language artifacts found. The malware continues to be actively distributed as of January 2025, focusing on expanding its victim pool and financial fraud.
🔖Rectifyq Taxonomies:
- relevancy: 🔴 Highly Relevant
- category: ⚔Threat
- sub-category: malware-analysis
- target: broad-based
- MY-relevancy: relevant
- action-taken: diamond-model
- topic: mobile-attack
🔖MISP Galaxies:
- producer= Kaspersky
- target-information=“Malaysia”
- target-information=“Brunei”
- country=“indonesia”
- online-service=“b0c71d51-34fd-47b5-9eb4-dd406ffc607f”
- mitre-attack-pattern=[‘T1582’, ‘T1636.002’, ‘T1660’, ‘T1481’, ‘T1422.001’, ‘T1417.002’, ‘T1626.001’, ‘T1636.004’]
MISP event uuid: 6ce88478-5011-443a-821c-02a5caf4fe00
Indicator of Compromise (IoCs)
type,value,comment
md5, 0e837107c42ee8282fd273e4a100b2de, ''
md5, 162ed054914a8c71ad02126693c40997, ''
md5, 3993142deafce26820411191e4fa9af8, ''
md5, 448fd25e24980bb0abd1208b0395a8e1, ''
md5, 4e7a72f32d5b6679a58c8261049d063b, ''
md5, 4ff2572a40300c0cce4327ec34259902, ''
md5, 5ed3ef03ca89c67bf93bb9230f5e4e52, ''
md5, 96143c28e7937f64ecdb6f87510afbbe, ''
md5, 9698fa3e7e64272ff79c057e3b8be5d8, ''
md5, 9a0147d4c9d6ed3be82825ce35fdb4ee, ''
md5, b8f4ac57c06755e98ecd263020aeaa82, ''
md5, daa30cd6699c187bb891448b89be1340, ''
md5, de9384577e28c52f8dc690b141098969, ''
md5, e4da1332303b93f11d40787f7a79b917, ''
md5, 43c6cb115876bf791a7816a3c7791ea8, 'No sample in VT\r\nLast check:08/02/2025'
md5, 6344466e975f89d8992080e2f0741661, 'No sample in VT\r\nLast check:08/02/2025'
Full IOCs available in Rectifyq’s MISP